Share
Executive Summary:
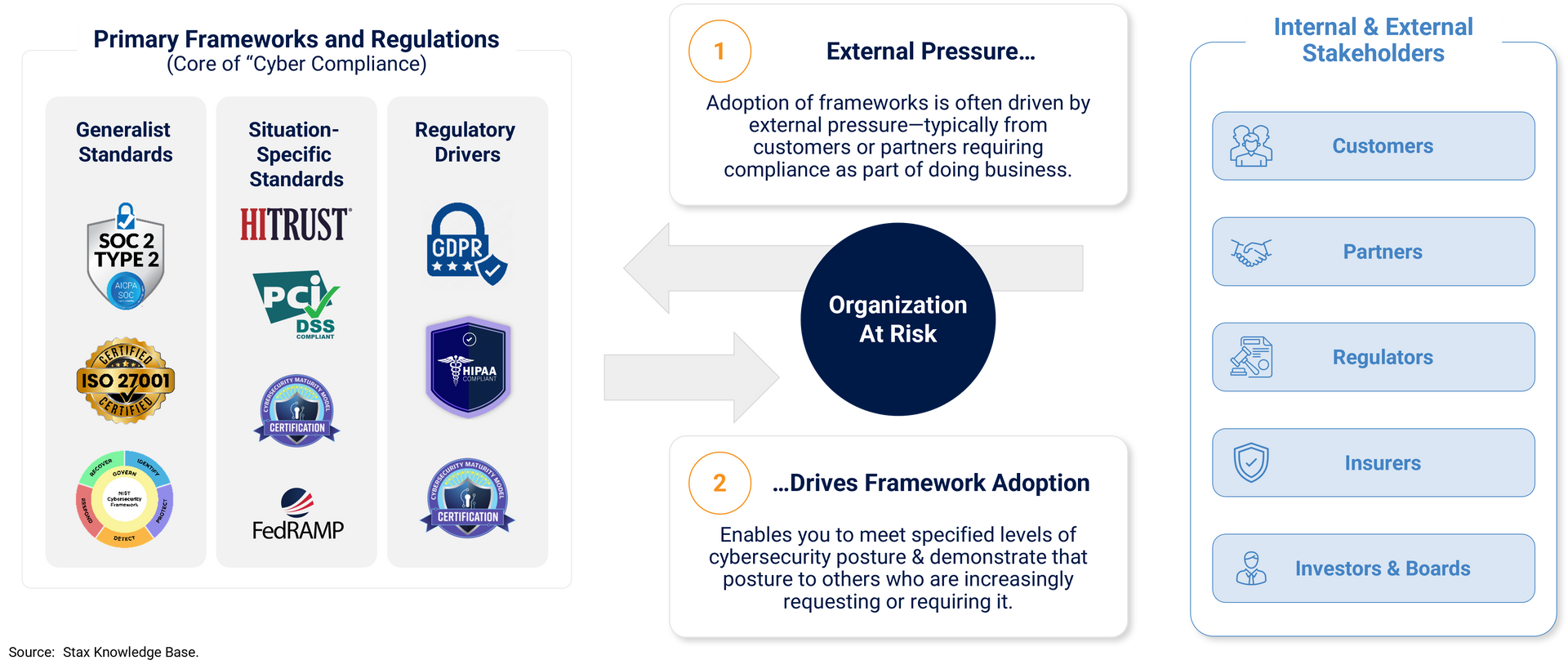
Cyber compliance is a fast-growing sector focused on helping organizations prove they meet cybersecurity and data protection standards as digital risk and complexity increase. Rising regulatory, contractual, and stakeholder pressures are driving widespread adoption across industries, reinforced by supply chain requirements. Achieving compliance requires ongoing investment across advisory, audit, and technology solutions, creating a large recurring spend base. For investors, the opportunity spans multiple segments, with value driven by positioning within the compliance lifecycle and alignment to in-demand frameworks.
Meet the Experts:
What is Cyber Compliance?
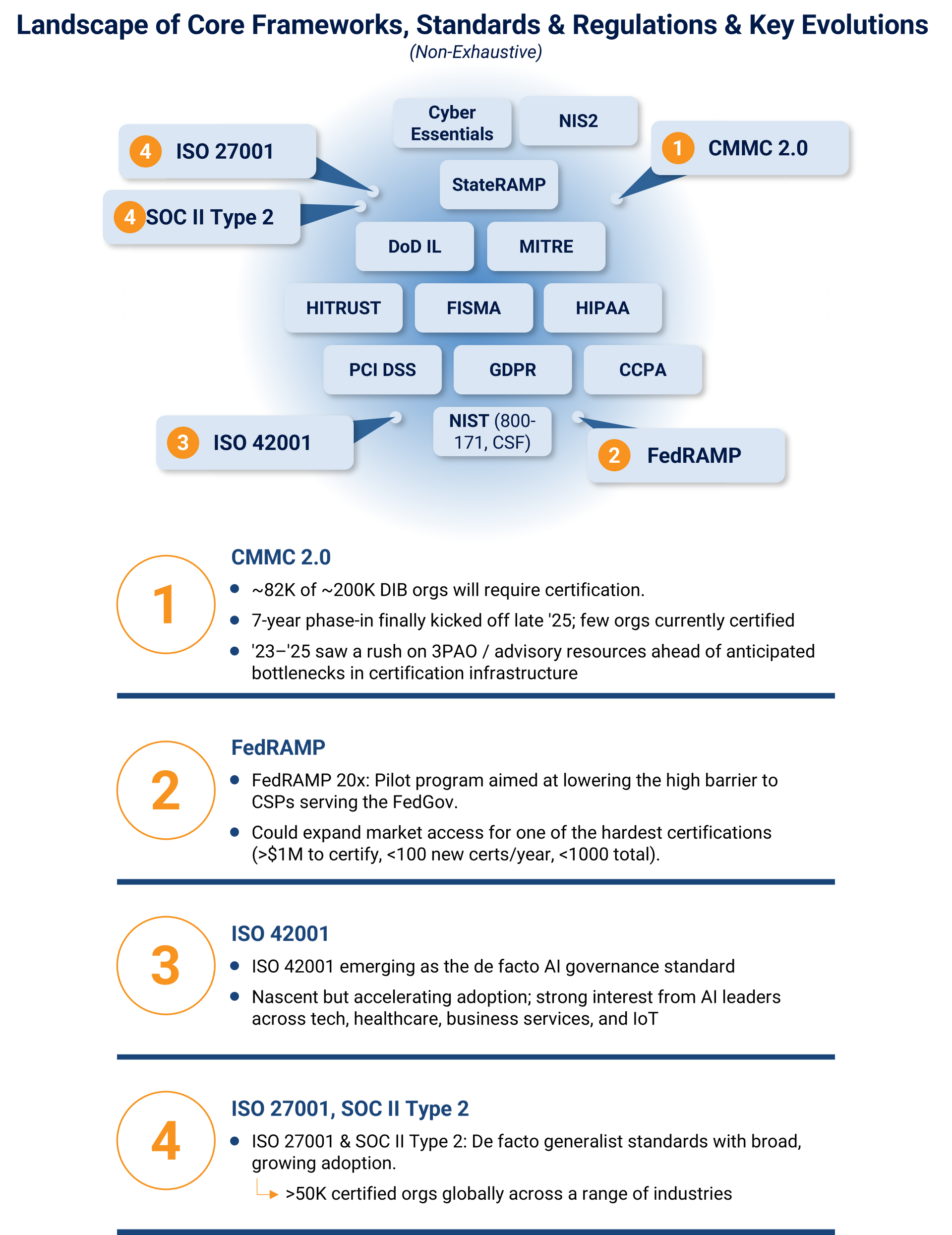
Cyber compliance is an organization’s ability to prove it meets established standards for cybersecurity and data protection, typically through third party audits or attestations against frameworks such as SOC 2 Type II, ISO 27001, HITRUST, CMMC, or emerging standards like ISO 42001 for AI systems.
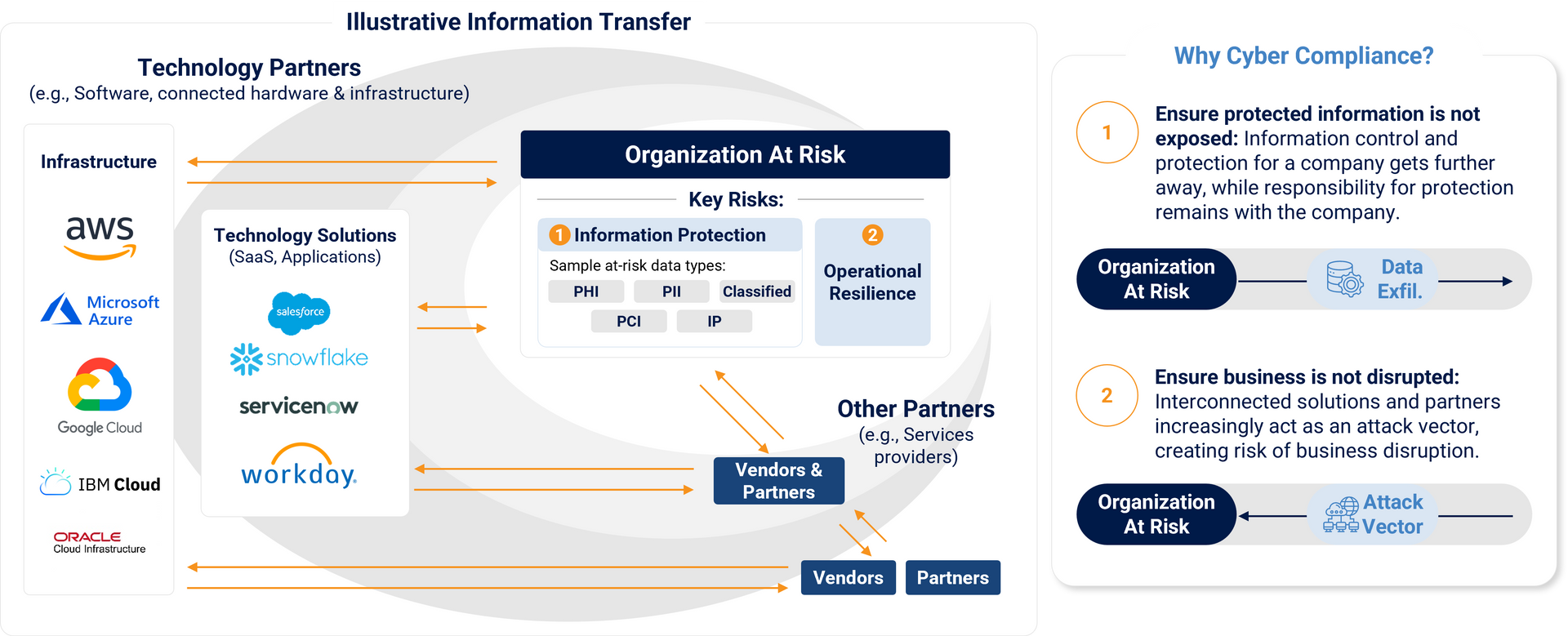
Modern organizations manage exponentially growing volumes of sensitive data and rely on a sprawling ecosystem of vendors, platforms, and service providers. Even small businesses often integrate with dozens of external systems. This expanding digital footprint creates two primary vectors of risk:
- Data exfiltration through insecure systems or data flows
- Unauthorized access to core technology via third party vulnerabilities
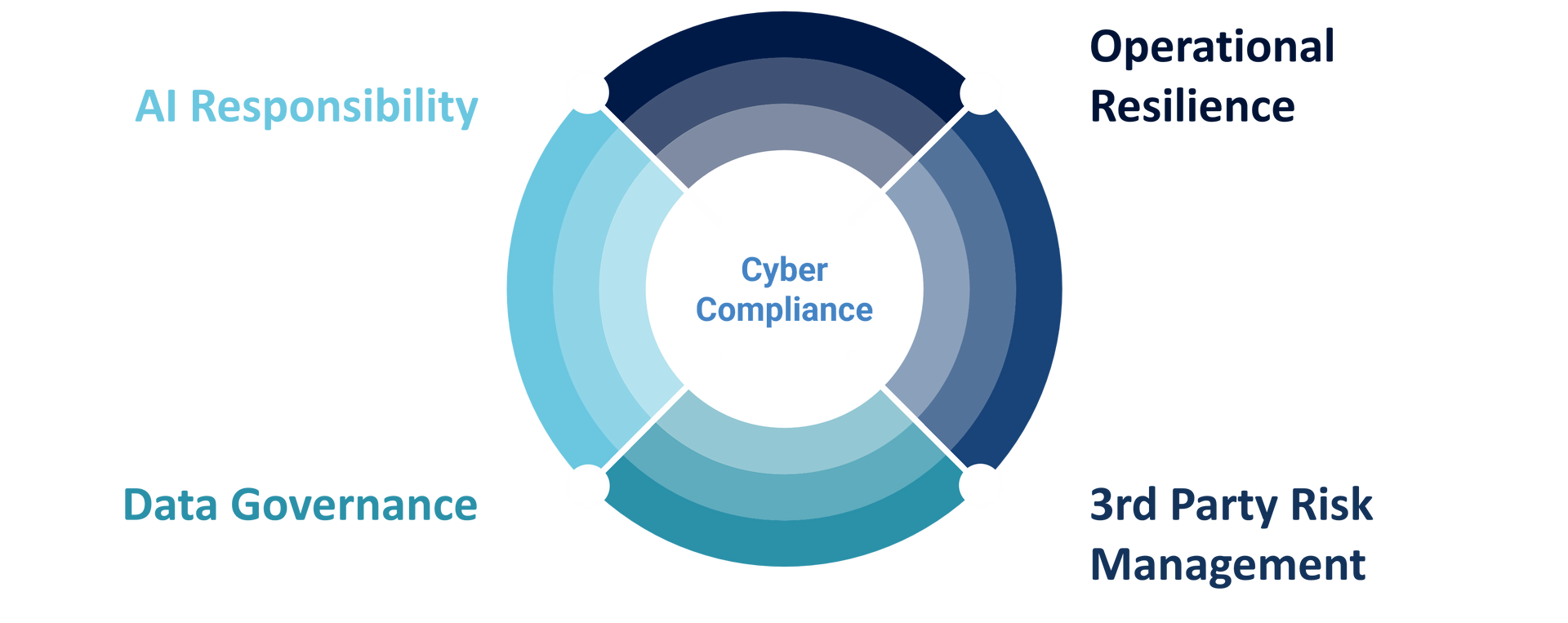
Cyber compliance sits at the center of operational resilience, third party risk management, data governance, and increasingly, AI responsibility.
It establishes a structured, auditable way to demonstrate that data and systems are protected—both within an organization and across its supply chain.
For investors, the software and services enabling this assurance have become a fast-growing, multibillion-dollar ecosystem. Adoption is accelerating across industries, expanding the landscape of attractive and differentiated opportunities.
Catalysts for Change
The era of implicit trust in cybersecurity is over. Self attestation is now widely viewed as inadequate, and stakeholders from enterprise customers and regulators to boards and investors are demanding verifiable proof of security posture.
Regulatory regimes such as HIPAA, GDPR, and CCPA impose significant penalties for security failures, yet most offer minimal prescriptive guidance on how to maintain compliance. As a result, many organizations only discover gaps in their posture after a breach or an enforcement action.
Conversely, platforms like CMMC, FedRAMP mandate intensive, prescriptive controls which can cost millions of dollars to certify and maintain.
Proactively demonstrating posture is often burdensome. Organizations may be required to complete hundreds of control checks, navigate 500 line spreadsheet questionnaires, undergo site visits and interviews, or pursue formal third-party certifications to validate their resilience.
[Additional Context: The U.S. Department of Defense’s CMMC 2.0 program emerged after audits revealed major discrepancies between contractors’ self‑attested compliance and their actual security posture, despite most existing control requirements being in place for years. The updated model now requires ~82,000 organizations handling mid‑ or high‑risk sensitive defense data (roughly 40% of the Defense Industrial Base) to obtain recurring third‑party certifications—representing tens of billions of dollars in projected economic impact.]
Cyber compliance frameworks codify best practices through hundreds of individual controls that address not only network or software security, but also physical safeguards, policy rigor, operational resilience, and vendor related risk. Together, these controls define what “good” looks like for an in-scope environment.
A broad mix of standards and regulatory drivers shape the landscape:
Framework Adoption Triggers Significant Spend
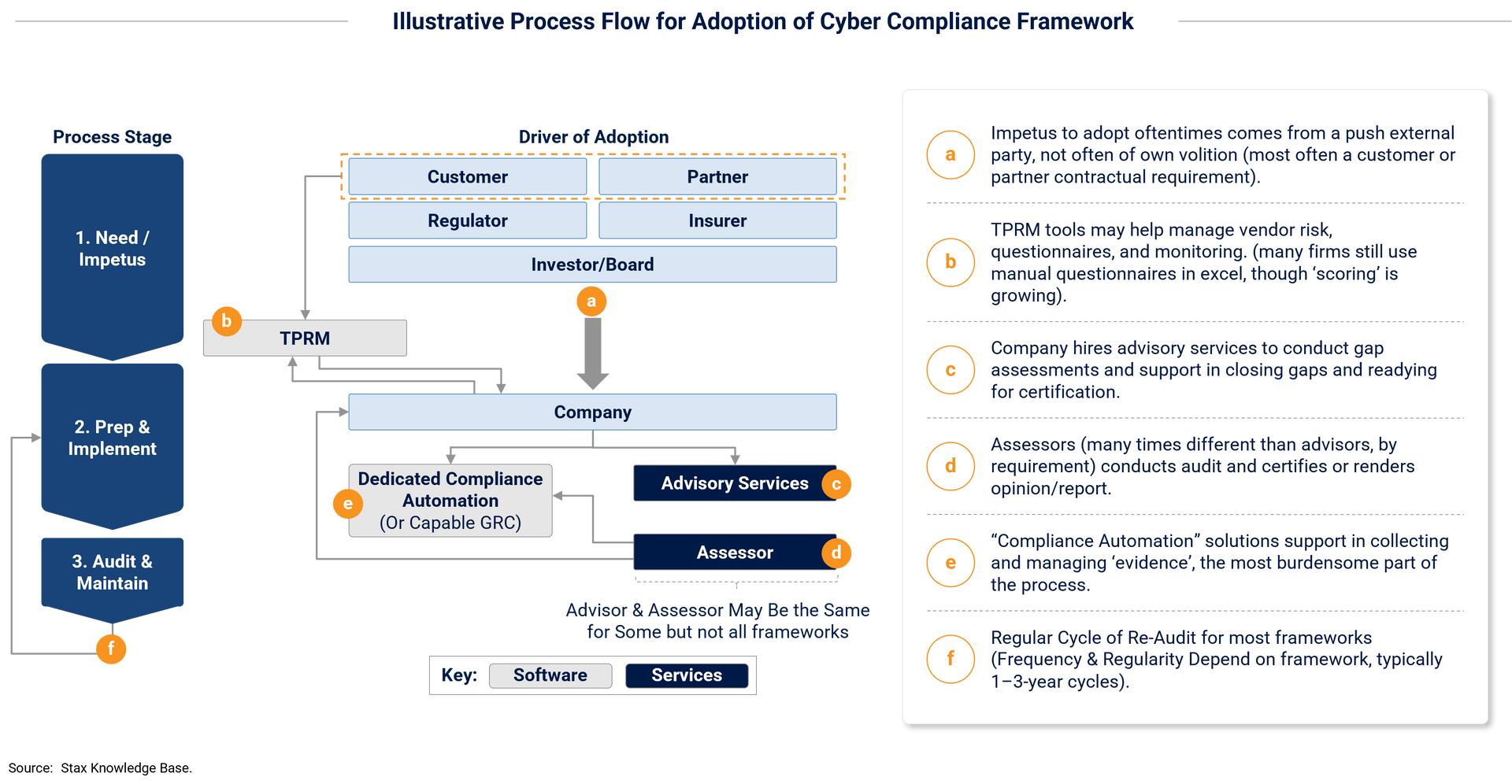
Cyber compliance is a multi-phase process that drives substantial investment across software and services.
The journey to certification or attestation typically includes 3 main phases:
- Pre‑audit preparation: The most resource‑intensive stage, often requiring advisory support for gap assessments, control mapping, remediation, and readiness activities. Depending on framework complexity, this phase can span from a few months to well over a year.
- Audit execution: Formal certification or attestation by accredited third‑party assessors.
- Post‑audit maintenance & Re-audit: Ongoing evidence collection, continuous monitoring (e.g., ConMon), reacting to business or framework changes (e.g., in-scope M&A), and periodic recertification to maintain compliance over time.
Total spend varies widely by framework and organizational complexity. A small company pursuing SOC 2 may invest $10K or less, while programs such as FedRAMP or CMMC can reach multi‑million‑dollar scale due to intensive advisory support, engineering effort, and specialized infrastructure requirements (e.g., GCC High environments).
Spending is typically front‑loaded, with the bulk of year‑one investment directed toward advisory and remediation work. However, recurring spend persists through annual or semiannual re‑audits, continuous monitoring, and ongoing technology needs. Software and tooling, particularly compliance automation, evidence management, and monitoring platforms, tend to represent recurring, multi‑year expenses.
A Variety of “Ways to Play”
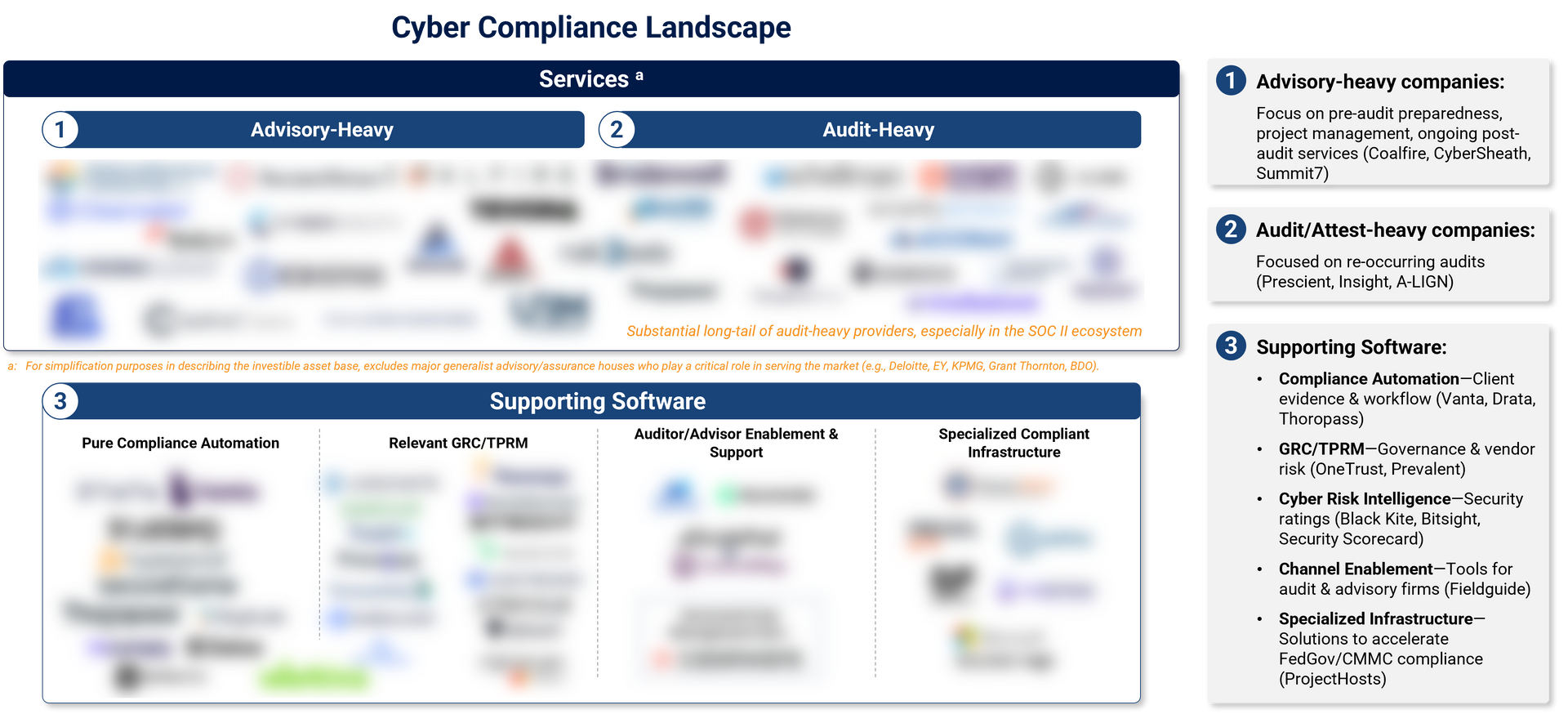
From an investment perspective, the cyber compliance ecosystem offers a broad range of entry points, with meaningful opportunities across services and technology. Key segments include:
- Advisory-focused services: Typically front-loaded, project-based spend, with some ongoing needs (e.g., continuous monitoring, program/infrastructure changes at re-audit cycles).
- Audit-focused services: Typically regular/re-ocurring, but lower levels of spend relative to advisory.
- Diverse set of supporting technology: Mix of compliance automation (on both the client side, and auditor side), TPRM and traditional GRC tools, and other supporting technology often needed throughout the compliance lifecycle.
Many companies offer a mix of advisory and audit services, though most index toward one or the other. Coalfire, Summit7, and ControlCase traditionally emphasize pre/post-audit advisory, while A-LIGN, Prescient, and Insight Assurance lean toward audit services.
Key Diligence Questions
Evaluating a cyber compliance asset requires a precise understanding of its positioning, market exposure, and structural advantages:
1. Define & understand the Target company's offering & alignment:
Revenue potential, addressable market, and growth trajectory, and ultimate value creation levers depend heavily on where the company sits in the compliance value chain and which frameworks it supports:
- What are the core / critical offerings are companies use from The Target?
- What frameworks / certifications, and thus market segments is The Target best aligned to?
- Which stages of the compliance journey does the company materially participate in (pre‑audit, audit, post‑audit)?
2. What are the revenue dynamics and pools we are exposed to as a result of our offering?
Various products, and frameworks have varied magnitudes of spend, spend curve shapes, and cadences and degrees of ‘re-occurrence’.
3. What is the corresponding market opportunity, and health based on our offering positioning?
Identifying the potentially addressable markets based on framework exposure, and other dynamics, is challenging but critical. Framework alignment is typically not defined along standard industry lines, but the prevalence of various characteristics (e.g., handling payment card data for PCI, selling products, tech, or services into the defense primes or subs for CMMC). Each framework and market niche has unique maturity levels, adoption velocities, and competitive intensity (e.g., ISO maturing rapidly in the U.S., PCI more mature globally, ISO 42001 and CMMC still nascent).
4. What defines our right-to-win in the markets we serve?
Audit-based services are heavily reliant on strong top-of-funnel (e.g., via partnerships with platforms like Vanta/Drata), while advisory partners rely on deep demonstrated subject-matter expertise, especially in complex implementations (e.g., FedRAMP, CMMC). Commoditization in certain market segments (e.g., workflow automation tech, lowest-end SOC II audits) can threaten to re-shuffle vendor positioning over the mid-term.
5. How strong is our commercial & GTM engine, truly?
Voice-of-customer/voice-of-partner research to establish and benchmark reputation, and delivery performance against key customer criteria are critical. Many companies across cyber compliance markets are currently ‘drinking from a firehose’. Performance benchmarking helps to define who is likely to remain successful as supply and demand trend closer towards equilibrium. Especially important in certain high-growth markets (e.g., CMMC).
6. What are the value creation levers we have access to based on our offering?
Cross-sell can be an attractive lever, and there is meaningful potential for accretive M&A for companies that clearly define their core competencies and offering set. These are shaped heavily by the nature of customer relationships and aligned markets (e.g., audit vs advisory, specific frameworks). There is no universal offering model, and many companies are still working to prove out effective and synergistic offering combinations. Assessing customer spend patterns, and appetite for ongoing or adjacent offerings is key.
7. How exposed are we to AI-driven market expansion vs. AI-driven commoditization?
AI is expanding compliance demand by introducing new risks and assurance surfaces (e.g., via ISO 42001), while simultaneously automating portions of readiness, evidence collection, and workflow execution. It’s key to understand whether the Target is positioned to capture incremental AI-driven spend, and to what extent AI is likely to erode differentiation or compress value/revenue capture in its core offerings.
Conclusion
Grant Thornton Stax’s cybersecurity and business services teams have supported more than 10 cyber compliance transactions over the past few years, including several of the sector’s most notable deals (A-LIGN, CyberSheath, HITRUST). If you’re evaluating a potential acquisition, exploring strategic growth opportunities, or preparing for a capital raise in this rapidly expanding market, let’s talk.
Reach out to Owen Tindle (otindle@stax.com) or Sam McCabe (smccabe@stax.com) to learn more.